Twitter announced a new policy that will remove text message two-factor authentication (2FA) from any account that doesn't pay for it.
In a blog post, Twitter said it will only allow accounts that subscribe to its premium Twitter Blue feature to use text-based 2FA. Twitter users who don't switch to a different type of two-factor authentication will have the feature removed from their accounts by March 20.
That means anyone who trusts that Twitter send a text message code to your phone to log in you will have your 2FA disabled, allowing anyone to access your accounts with just a password. If you have a password easy twitter If you guess or use that same password on another site or service, you should take action as soon as possible.
Twitter claims that is Committed to keeping people safe and secure on Twitter. This is not true. Instead, you're looking at one of the dumbest security decisions ever made by a company in real time.
It is not clear for what reason this new 2FA policy, first revealed by Zoë Schiffer from platforms and later confirmed by Twitter, it was instituted. Since Elon Musk's $44 billion acquisition, Twitter has been generating cash and talk about the template. The decision to remove SMS 2FA was likely to save the company money, since texting isn't cheap. Twitter cannot be called to account as Musk fired the entire communications team.
Twitter justified the decision in your blog post, saying that bad actors can abuse SMS 2FA. This could refer to SIM swapping attacks, where a hacker convinces their mobile phone provider to assign a victim's phone number to a device controlled by the hacker. By taking control of a person's phone number, the hacker can impersonate the victim, as well as receive text message codes that can Allow you to access the victim's online accounts. But making SMS 2FA available only to subscribers of Twitter Blue does not make users that pay are more protected against SIM swapping attacks. In any case, by encouraging paid users to trust SMS 2FA, their twitter accounts are more prone to takeovers if your phone number is hijacked.
Having said all of that, and this is important, SMS 2FA still provides much greater protections for your accounts than not using 2FA at all. But the new policy Twitter is not the way to encourage users to use a more secure 2FA. In fact, companies like Mailchimp take the opposite (but correct) approach to encourage users to activate 2FA by discounting customers' monthly bills.
The positive side, if we can call it that, is that twitter is not removing 2FA altogether. You can still protect your account with strong 2FA without paying a penny to Elon Musk.
Regardless of whether or not you have abandoned your account Twitter in favor of alternative services and decentralized ones like Mastodon and others, you'll still want to take steps before March 20 to protect your account in case someone breaks in and starts tweeting on your behalf.
Instead of using 2FA codes sent via text, you need app-based 2FA, which is much more secure and is as fast as receiving a text. (Many online sites, services, and applications also offer 2FA based in applications). Instead of sending a code to your phone via text message, you can generate a code via an app authentication methods on your phone, such as Duo, Authy, or Google Authenticator. to name a few. this is so much more sure since the code never exits your device.
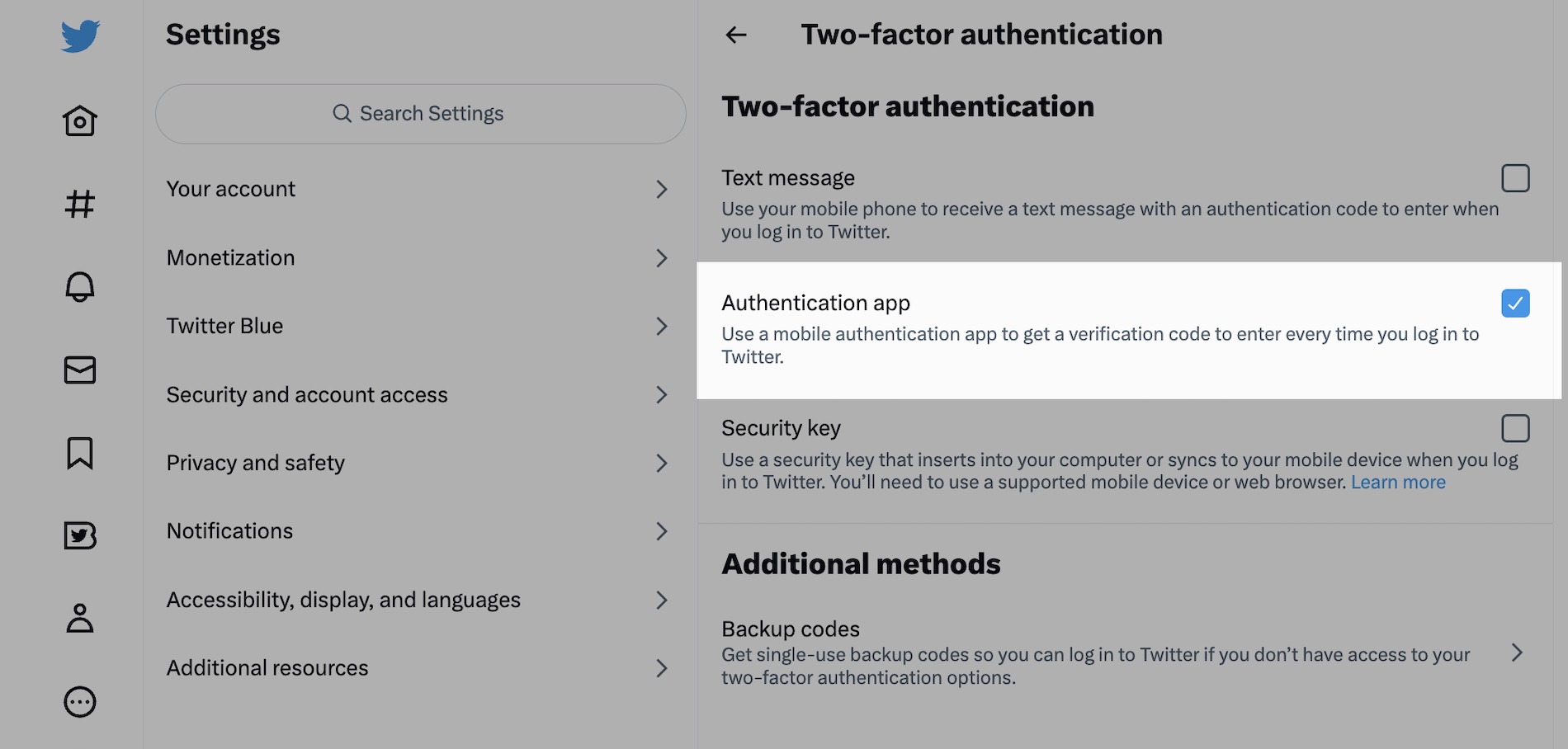
To set this up, first make sure you have your authenticator app installed on your phone. Go to your Twitter account, then go to Settings and privacy, then Account access and security and finally Security. Once you're in the Two factor authentication, then select authentication app. Follow the instructions carefully; you may need to enter your account password to get started. Once you're done, you'll be able to sign in with your password, then a code generated from your authenticator app.
Remember, because this is a much more secure access to your Twitter account, which means that if you lose your phone it can be very difficult to access your account again. That is why you should keep a record of your backup codes, which allow you to gain access to your account if you are locked out, safely stored in your password manager. You can find your backup codes in the same place where you set up your app-based 2FA.




